Subaskaran Allirajah is the founder of Lycamobile and a Bollywood producer. 
Regulatory & Politics
Lycamobile tries to kill T-Mobile's Mint Mobile acquisitionLycamobile tries to kill T-Mobile's Mint Mobile acquisition
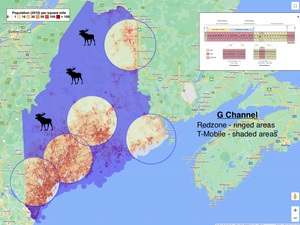
T-Mobile's proposed $1.35 billion purchase of Mint Mobile is facing mounting delays. Now, a T-Mobile MVNO called Lycamobile has launched a public campaign against the deal.
Subscribe and receive the latest news from the industry.
Join 62,000+ members. Yes it's completely free.
































.png?width=300&auto=webp&quality=80&disable=upscale)










